Recently, a customer called me to configure Netflow on these routers because he just installed NetFlow Analyzer software from ManageEngine. This software is an “all in one” NetFlow collector, database, WebUI software, able to build pretty nice reports.
In my opinion, Netflow is one of the absolutely required software to have a good visibility when you operate a network.
NetFlow, Flexible NetFlow (FNF), IP Flow Information Export (IPFIX)
NetFlow is a Cisco technology available in Cisco IOS since 1996. It provides statistics on packets flowing through a router or a switch. NetFlow collect and export the data to enable network and security monitoring, network planning, traffic analysis, and IP accounting.
Flexible NetFlow (FNF) improves the original NetFlow by adding the capability to customize the traffic analysis parameters for your specific requirements. Flexible NetFlow facilitates the creation of more complex configurations for traffic analysis and data export through the use of reusable configuration components.
FNF is supported (at least) on the following Cisco platforms: ISR, ISR-G2, ISR4K, ASR1K, ASR9K, CRS-1, CSR1000v, Catalyst 3750X, 3560X, 3850, 4500 & 6500 SUP2T, Nexus 7K, Nexus 1000V. It is available since IOS 12.4(9)T for some platforms, or IOS 15.0(1)M for others (from 12.2(50)SY on 6500/Sup2T). So since a very long time.
IP Flow Information Export (IPFIX) is the IETF standard version of NetFlow. There are changes in the terminology but this is the same principles like Cisco NetFlow version 9.
Flow Exporter, Record, Monitor and Activation.
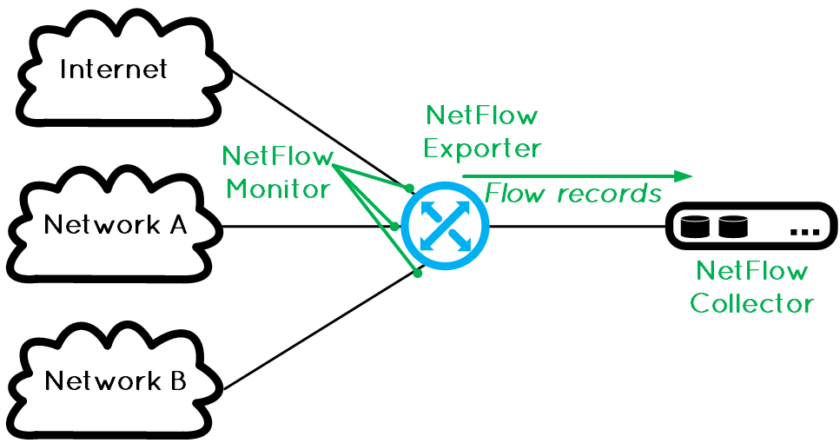
FNF is divided into three distinct functions: the selection of data we want to analyse (flow record), the collection of the data (flow monitor), and the export of the data to a collector (flow export). To complete the configuration, a flow monitor can be applied to one or multiple interface(s).

Flow Record
Flow records are used to analyze traffic data for a specific purpose. A customized flow record must have at least one match criterion for use as the key field and typically at least one collect criterion for use as a non-key field. There are hundreds of possible permutations of customized flow records:
Router(config)# flow record my-record Router(config-flow-record)# match <-- Specify a Key Field Router(config-flow-record)# collect <-- Specify a Non-Key Field Router(config-flow-record)# match ? application Application Fields datalink Datalink(layer 2) fields flow Flow identifying fields interface Interface fields ipv4 IPv4 fields ipv6 IPv6 fields routing routing attributes transport Transport layer field Router(config-flow-record)# collect ? application Application Fields counter Counter fields datalink Datalink(layer 2) fields flow Flow identifying fields interface Interface fields ipv4 IPv4 fields ipv6 IPv6 fields routing IPv4 routing attributes
Please refer to the Cisco IOS Flexible NetFlow Command Reference for the complete list of key and non-key fields.
Flow Export or Exporters
Flow exporters are created as separate components in a router’s configuration. Exporters are assigned to flow monitors to export the data from the flow monitor cache to a remote system such as a NetFlow collector or the Netflow Analyser of my customer. Flow monitors can support more than one exporter. Each exporter can be customized to meet the requirements of the flow monitor or monitors in which it is used and the NetFlow collector systems to which it is exporting data.
Flow Monitor
Each flow monitor has a separate cache assigned to it. Each flow monitor requires a flow record to define the contents and layout of its cache entries. These record formats can be one of the predefined formats or a user-defined format. In the flow monitor we also specify the exporter(s) we will use.
Activation per Interface
The start the show, we finally must activate the flow monitor on an Interface. This is the most simple configuration:
Router(config-if)# ip flow monitor my-monitor [input | output] [unicast | multicast]
Flexible NetFlow configuration example
Here is an example of configuration I used to export netflow datas to ManageEngine Netflow Analyser. This configuration was made on a 6500/SUP2T.
flow exporter EXPORTER description --- To NetFlow Analyser Software --- destination 10.10.10.10 source Loopback0 transport udp 9996 template data timeout 60 ! flow record NETFLOW-RECORD match ipv4 protocol match ipv4 source address match ipv4 destination address match transport source-port match transport destination-port match interface input collect routing source as collect routing destination as collect routing next-hop address ipv4 collect ipv4 source mask collect ipv4 destination mask collect transport tcp flags collect counter bytes long collect counter packets long collect timestamp sys-uptime first collect timestamp sys-uptime last ! flow monitor NETFLOW-MONITOR exporter EXPORTER cache timeout active 60 cache timeout inactive 15 record NETFLOW-RECORD ! int ten1/2/3 ip flow monitor NETFLOW-MONITOR input !
Go further
This is one flexible NetFlow configuration example, but we can go much further.
Flexible NetFlow with NBAR Integration
We can, for example, add the power of NBAR2 into a FNF configuration:
router(config)# flow record app_record router(config-flow-record)# match interface input router(config-flow-record)# match ipv4 source address router(config-flow-record)# match ipv4 destination address router(config-flow-record)# match application name account-on-resolution ! match "application name" calls NBAR "account-on-resolution" (ASR1K). router(config-flow-record)# collect counter packets router(config-flow-record)# collect counter bytes router(config)# flow exporter app_collector router(config-flow-exporter)# destination <ip address> router(config-flow-exporter)# option interface-table router(config-flow-exporter)# option application-table router(config-flow-exporter)# option application-attributes router(config-flow-exporter)# option sub-application-attributes ! The last three lines export the full list of applications and the full list of attributes per app. router(config)# flow monitor app_monitor router(config-flow-monitor)# record app_record router(config-flow-monitor)# exporter app_collector router(config-flow-monitor)# cache timeout event transaction-end
Then, we can see the application on the netflow collector or directly into the cache of the router:
router# show flow mon app_mon cache IPV4 SRC ADDR IPV4 DST ADDR APP NAME … =============== =============== =============== 10.0.1.1 10.0.1.2 nbar edonkey 10.0.1.1 10.0.1.2 nbar ssh 10.0.1.1 10.0.1.2 nbar http 10.0.1.1 10.0.1.2 NBAR custom-app
In the output above: nbar (lowercase) = standard applications and NBAR (uppercase) = custom applications.
Top Talkers
This command is also very useful to see, for example, the top-10 IP addresses that are sending the most packets:
Router# show flow monitor <monitor> cache aggregate ipv4 source address sort highest counter bytes top 10
Or the top-5 destination addresses to which we are routing most traffic from the prefix 10.10.10.0/24:
Router# show flow monitor <monitor> cache filter ipv4 destination address 10.10.10.0/24 aggregate ipv4 destination address sort highest counter bytes top 5
Or the top-10 protocols:
Router#show flow monitor <monitor> cache aggregate ipv4 protocol sort highest counter bytes top 10
The applications are without limits!